Bi-monthly news update from IsDB-BISEW IT Scholarship Programme (January 2026)
Apr 07, 2026 / IT Scholarship ProgrammeEmpower

Welcome to the January 2026 issue of Empower, the periodic newsletter of the IsDB-BISEW IT Scholarship Programme. This edition features the following topics of note:
- Understanding Web Application Architectures
- In Their Own Words – Kazi Abu Sayeed’s Story
Understanding Web Application Architectures: A Comprehensive Overview of Infrastructure Models and Components
No web application is identical. The market creates web applications for a multitude of uses and purposes. Applications are developed and programmed differently, and the backend infrastructure can be configured in different ways.
It’s important to understand the various types of web applications that run behind the scenes, their structure and components, and how they can be configured within a company’s infrastructure.
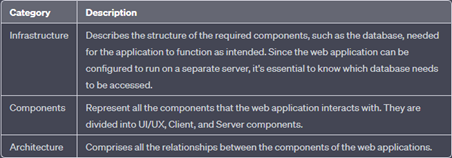
The layouts of web applications consist of different layers that can be organised into three main categories:
Web Application Infrastructure
A web application can use various infrastructure configurations, also known as models.
The most common ones can be grouped into four types:
- Client-Server
- One server
- Multiple servers — One database
- Multiple servers — Multiple databases
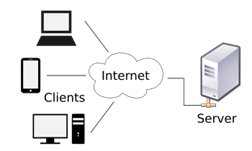
Client-Server
Web applications often adopt the client-server model. A server hosts the application in a client-server model and distributes it to numerous clients attempting to access it.
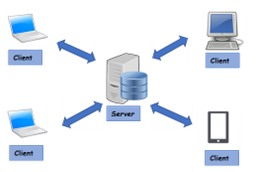
In this model, web applications have two types of components: those in the front end, which are usually interpreted and executed on the client side (browser), and the back-end components, which are usually compiled, interpreted, and executed by the hosting server.
When a client visits the web application through the URL, the server uses the application’s main user interface (UI).
As soon as the user clicks a button or requests a specific function, the browser sends an HTTP web request to the server, which interprets the request and performs the necessary tasks to complete the request (e.g., log in the user, add an item to the cart, navigate to another page, etc.).
Once the server has the necessary data, it sends the result back to the client’s browser, displaying the result in a format that is understandable to the user.
One server
In this architecture, the entire application or several applications and their components, including the database, are hosted on a single server. Although the design is straightforward to implement, it is also the riskiest.
If any application hosted on this server is compromised in this architecture, then all application data will be compromised. This design represents the saying “Don’t put all your eggs in one basket”, as any vulnerable hosted application compromises the entire server.
In addition, if the web server goes down and becomes unavailable for any reason, all hosted applications also become unavailable until the problem is resolved.
Multiple servers — one database
This model separates the database into its server and allows the hosting server of the applications to access the database server to store and retrieve data.
It can be seen as multiple servers for one database or one server for one database, as long as the database is separated into a dedicated (own) server.

This model allows multiple applications to access a single database to retrieve the same data without requiring data synchronisation. The applications can be replicas of a main application (e.g. primary/backup), or they can be separate applications that share the same data.
The main advantage of this model (from a security perspective) is segmentation, where each component of a web application is located and hosted separately. If a web server is compromised, the others are not directly affected.
Similarly, if the database is compromised (e.g. by a SQL injection), the web application is not directly affected. Access control measures still need to be implemented after asset segmentation, such as limiting web application access to only the data necessary for it to function as expected.
Many servers — many databases
This model is built on top of the “many servers, one database model”. However, with the database server, each web application is hosted on a separate database.
The web application can only access private data and data that is shared across applications. It is also possible to host each web application’s database on its server.
This design is also widely used for redundancy, so if any web server or database goes offline, a backup will take over to reduce downtime as much as possible.

Downtime — the period during which a system is unavailable or offline. It can happen due to an unexpected issue or scheduled maintenance. Do you remember when Facebook services went down? That was a downtime that cost them $$$$ in losses.
While it can be difficult to implement and requires tools like load balancers to function correctly, this architecture is one of the best choices in terms of security due to its proper access control measures and asset segmentation.
In addition to these models, there are other web application models, such as the serverless model or applications that use microservices.
Components of web applications
Each application can have a different number of components. All components of the previously mentioned model can be divided into:
- Client
- Server → Web server → Web application logic → Database (DB)
- Services (microservices) → Integration with third-party services → Integration with web applications
- Serverless functions
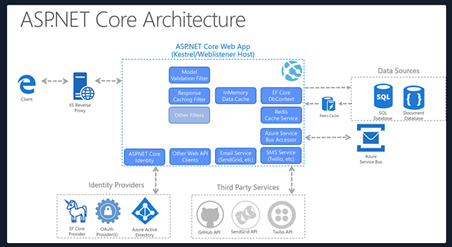
The architecture of web applications
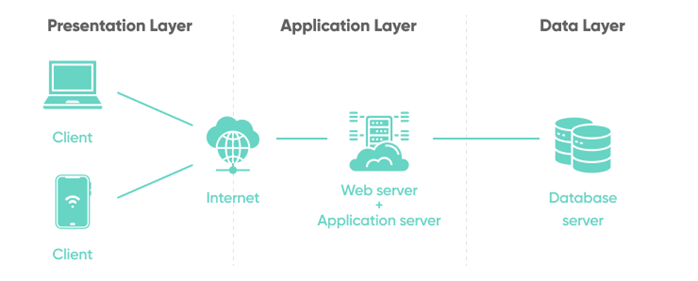
The components are divided into three different layers:
Presentation layer — consists of UI process components that allow communication with the application and system. They can be accessed by the client through the browser and are returned in the form of HTML, CSS, and JS.
Application layer — Ensures that all web requests (client) are processed correctly. Several criteria are checked, such as authorisation, privileges, and the data passed to the client.
Data layer — Works together with the application layer to determine where the required data is stored and can be accessed.
An example of a web application architecture would look something like the following figure:
Microservices
We can think of microservices as independent components of the application, where in most cases they are programmed for a single task.
For example, in an online store, we can break down main tasks into the following components:
- Registration
- Search
- Payments
- Rating
- Reviews
These components communicate with each other and with the client. Communication between microservices is called stateless, meaning that the request and response are independent. This is because the data stored is kept separate from the respective microservices. The use of microservices is considered an SOA — Service-oriented architecture, built as a collection of different automated functions focused on a single business objective. Moreover, these microservices depend on each other.
Another essential and efficient component of microservice is that they can be programmed in different languages and still interact. They benefit from easily scalable and rapidly developed applications, which encourage innovation and accelerate the delivery of new features to the market.
Some benefits are:
- agility
- flexible scaling
- easy deployment
- reusable code
- resilience
Serverless
Cloud providers like AWS, GCP, and Azure, among others, offer serverless architecture services. These platforms provide application frameworks for building web applications without worrying about servers.
These applications then run on serverless containers (like Docker). This type of architecture gives the company the flexibility to build and deploy applications and services without managing the infrastructure. All server management is done by the cloud provider, eliminating the need to provision, scale, and maintain the servers needed to run applications and databases.
Architecture Security
Understanding the general architectures of web applications and each specific design is important when performing a pentest on any application. In many cases, an individual vulnerability may not necessarily have been caused by a programming error, but by an error in the design of its architecture.
For example, a web application may have all its main functionalities well implemented. However, due to a lack of access control measures in its design, such as the use of RBAC, users may access administrator functions that were not programmed to be accessed directly by them or even access private information from other users without privileges to do so.
To fix this type of error, a significant change in the design would be necessary, which would be both costly and labour-intensive.
Another example would be if we couldn’t find the database after exploiting a vulnerability and gaining access through the back-end server, which could indicate that the database is hosted on a separate server.
We might only find part of the database data, which may indicate that multiple databases are being used.
That’s why security needs to be considered at every stage of web application development, and penetration testing should occur throughout the development lifecycle.
In Their Own Words – Kazi Abu Sayeed’s Story
Junior Dot NET Developer
Global MediKlaud (BD) Ltd
IsDB-BISEW IT Scholarship Programme: Round-63
Course: Cross-Platform Apps using ASP.NET, Angular & React
Kazi Abu Sayeed’s professional journey demonstrates how structured technical training can open entirely new career pathways. Although deeply involved in humanitarian and social initiatives during his early years, it was the training provided by the IsDB-BISEW IT Scholarship Programme that enabled him to successfully transition into the information technology sector.
Born in Madaripur, Abu Sayeed later moved to Dhaka with his family. He completed his SSC and HSC examinations at Dhanmondi Government Boys’ High School and went on to study Physics at Dhaka College, earning both his bachelor’s and master’s degrees in the subject, completing the latter in 2021. Alongside his academic pursuits, he was actively engaged in social work. While still an undergraduate, he co-founded the humanitarian organisation Mastul Foundation, which has since become widely recognised. He later established Stand Bangladesh, an organisation dedicated to supporting children’s education and promoting income-generating opportunities for the urban poor.
His experience in social development work helped him secure a role as an Education Coordinator at the JAAGO Foundation in Madaripur. However, his career took a decisive turn when he came across a Facebook advertisement for the IsDB-BISEW IT Scholarship Programme. Already aware of the programme’s strong reputation for professional IT training, he applied and successfully passed the competitive selection process. He was subsequently admitted to the course titled “Cross-Platform Apps using ASP.NET, Angular & React.”
The training proved to be a transformative experience. While the introductory module on computer fundamentals was familiar to him due to his previous office experience, subsequent modules introduced entirely new areas of learning. The database module, particularly SQL and Microsoft SQL Server, initially presented a significant challenge but also sparked his interest in software development.
Under the close guidance of experienced instructors, complex topics were taught through a carefully structured combination of lectures and extensive hands-on practice. As the course progressed, Abu Sayeed received comprehensive training in web and mobile application development using modern frameworks and tools. He found the programme both demanding and intellectually stimulating, and credits its practical, project-based methodology with helping him develop strong technical and problem-solving skills. His final class project received considerable appreciation and remains publicly available online.
After successfully completing the 10-month training programme in August 2025, Abu Sayeed benefited from the support of the Placement Cell of the IsDB-BISEW IT Scholarship Programme, which helped him secure a position as a Junior .NET Developer at Global MediKlaud (BD) Ltd in December 2025.
At Global MediKlaud, he works as part of a development team building and implementing an Enterprise Resource Planning (ERP) system for a major trade organisation. Notably, one of the company’s directors is also a graduate of the IsDB-BISEW IT Scholarship Programme, reflecting the programme’s strong presence within the industry.
Reflecting on his experience, Abu Sayeed states:
“Participating in the IsDB-BISEW IT Scholarship Programme has been one of the most important decisions of my life. I would highly recommend it to anyone who wishes to build a professional career in information technology.”
Abu Sayeed’s story illustrates the transformative role that high-quality technical training and industry-oriented education can play in enabling talented individuals from diverse backgrounds to establish successful careers in the IT sector.